Session tokens provide temporary credentials with automatic expiration.
Use cases
- Local development and testing
- CI/CD pipelines requiring credential rotation
- Environments with compliance requirements for time-limited access (typically 1-12 hours)
Prerequisites
Before generating session tokens, ensure you have:
- AWS CLI installed and configured
- An existing IAM role you can assume
- Your New Relic account ID
Generate temporary credentials
Open your terminal and run this command (replace with your role ARN):
aws sts assume-role \--role-arn "arn:aws:iam::YOUR_ACCOUNT:role/YOUR_ROLE" \--role-session-name "WorkflowAutomationSession"If this is your first time using AWS CLI, you may need to configure it with
aws configureand enter your access credentials: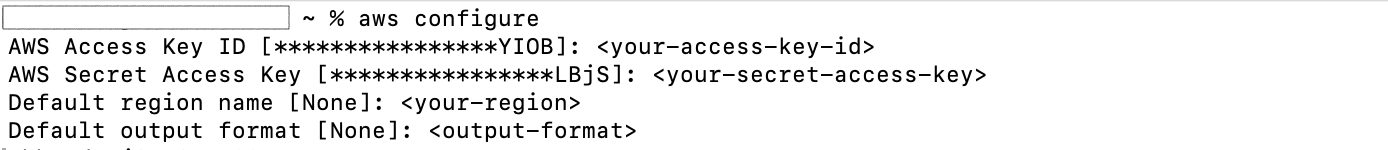
AWS returns three values—you need all three:
{"Credentials": {"AccessKeyId": "ASIAIOSFODNN7EXAMPLE","SecretAccessKey": "wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY","SessionToken": "FQoGZXIvYXdzEBk...","Expiration": "2025-01-25T12:00:00Z"}}Store all three credentials in secrets manager:
AccessKeyIdstore asawsAccessKeyIdSecretAccessKeystore asawsSecretAccessKeySessionTokenstore asawsSessionToken注意
Session tokens expire (typically after 1 hour). Set a reminder to refresh them before the
Expirationtimestamp, or your workflows will fail with authentication errors.